Advanced encryption standard based on key dependent S‐Box cube - Seghier - 2019 - IET Information Security - Wiley Online Library
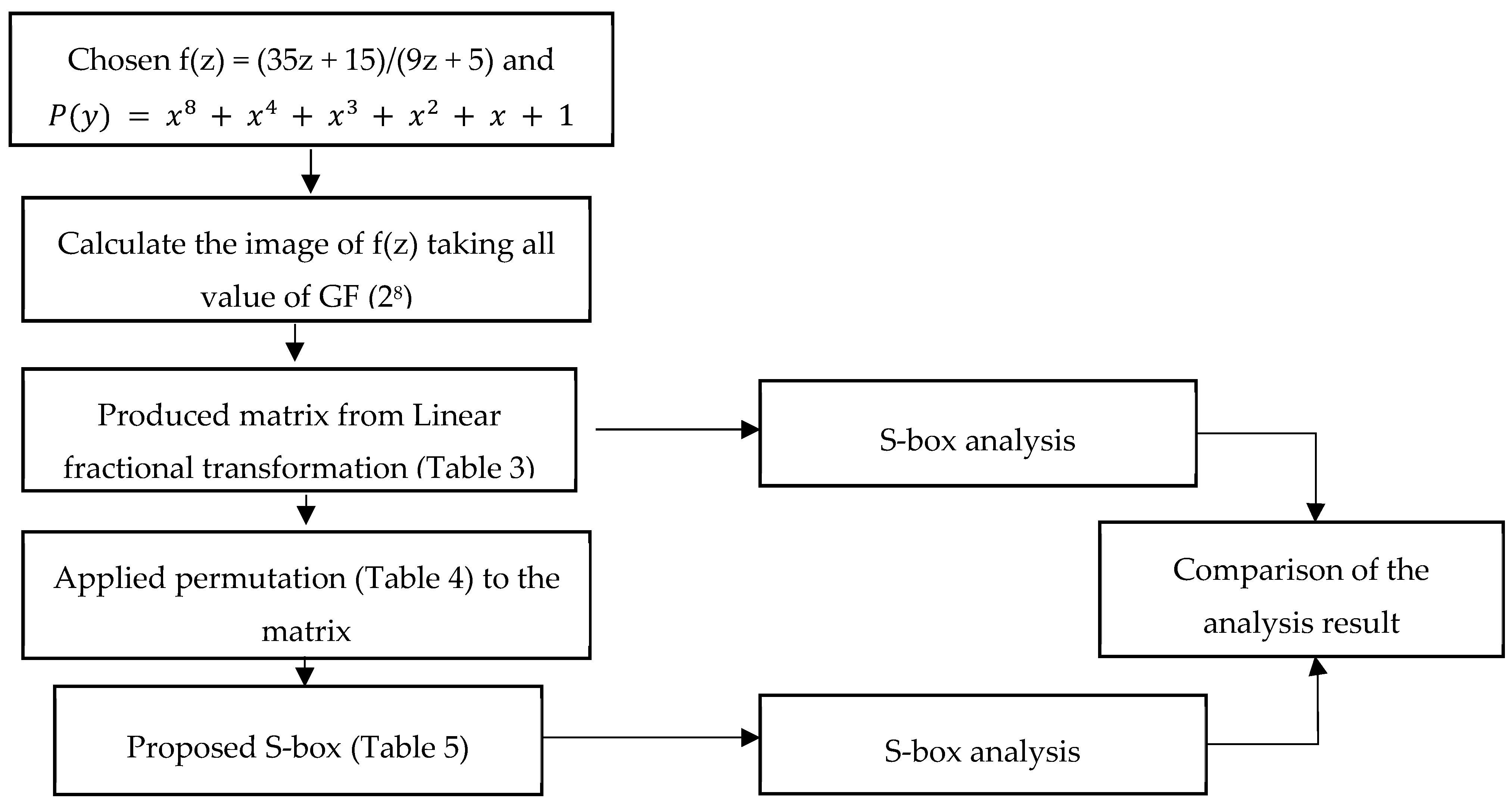
Symmetry | Free Full-Text | S-box Construction Based on Linear Fractional Transformation and Permutation Function
S-box Construction Based on Linear Fractional Transformation and Permutation Function. - Document - Gale Academic OneFile

Symmetry | Free Full-Text | S-box Construction Based on Linear Fractional Transformation and Permutation Function
![A novel systematic byte substitution method to design strong bijective substitution box (S-box) using piece-wise-linear chaotic map [PeerJ] A novel systematic byte substitution method to design strong bijective substitution box (S-box) using piece-wise-linear chaotic map [PeerJ]](https://dfzljdn9uc3pi.cloudfront.net/2022/cs-940/1/fig-3-2x.jpg)

![PDF] AN IMPROVED AES S-BOX AND ITS PERFORMANCE ANALYSIS | Semantic Scholar PDF] AN IMPROVED AES S-BOX AND ITS PERFORMANCE ANALYSIS | Semantic Scholar](https://d3i71xaburhd42.cloudfront.net/af65a349981b8c3ef96c1f7725ba78c398aba27b/11-Table7-1.png)



![PDF] On the Boomerang Uniformity of Cryptographic Sboxes | Semantic Scholar PDF] On the Boomerang Uniformity of Cryptographic Sboxes | Semantic Scholar](https://d3i71xaburhd42.cloudfront.net/477a337174b5bd8feabb3e27d4421f4f29454c40/4-Figure3-1.png)